Darknet Markets 2026:
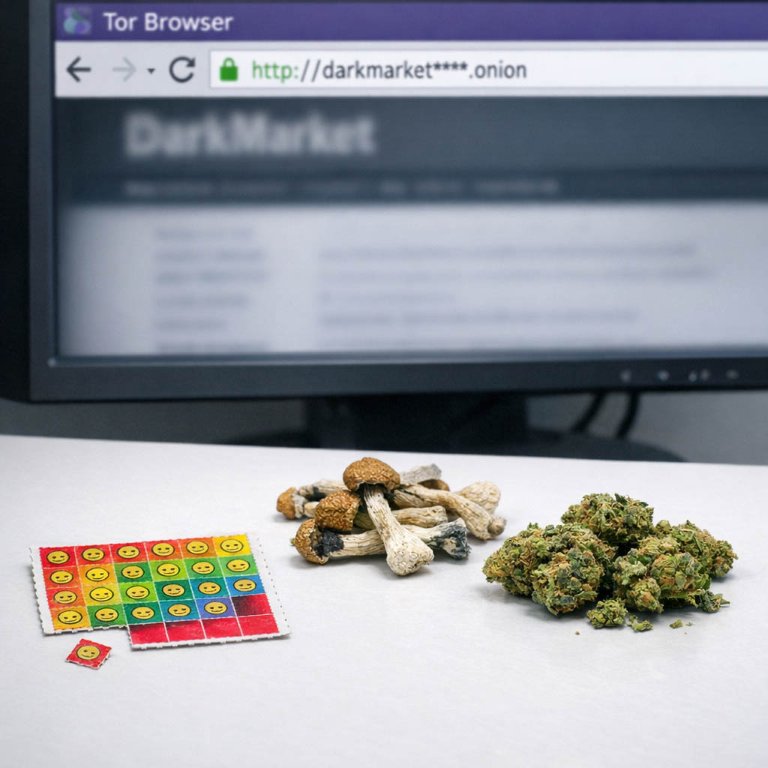
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-04-29
Finding Trusted Darknet Markets for Safer Shopping
Accessing a darknet marketplace begins with obtaining a direct link or mirror from a reliable source. These links are distributed through forums and specialized link directories to circumvent the dynamic nature of darknet addresses. The primary function of a verified link is to connect the user to a platform where vendor verification processes are already in place. These platforms implement a system where sellers must often provide a deposit and undergo a screening period before listing items, which establishes a baseline of market accountability.
Upon entering a marketplace via a trusted link, the structure facilitates efficient trade. Product listings are organized into categories, and each vendor profile is accompanied by a detailed feedback score and written buyer reviews. This system transforms user experience into a quantifiable metric. A vendor with a high number of completed transactions and positive reviews is statistically more likely to deliver the advertised product quality. The review system covers specific aspects of the transaction:
- The accuracy of the product description and weight.
- The stealth and discretion of the packaging.
- The speed and reliability of shipping.
- The purity or potency of the product, often confirmed by third-party testing services discussed in forum communities.
This environment allows for informed purchasing decisions. Buyers can cross-reference a vendor's reputation across multiple forums and marketplaces, creating a comprehensive picture of reliability. The integration of an escrow system further secures the transaction. Funds are held by the marketplace until the buyer confirms satisfactory receipt of the product, at which point the vendor is paid. This mechanism significantly reduces the risk of fraud and incentivizes vendors to maintain high standards, as their business viability depends on consistently releasing escrow funds through successful completions.
How Darknet Markets Make Buying Drugs Easy and Safe
The operational efficiency of darknet markets is fundamentally linked to the systematic vetting of access points and participants. A user's primary task is to find trusted darknet links through dedicated forums and review sites, which act as community-driven directories. These verified gateways are the first filter, ensuring a direct connection to the intended platform and mitigating the risk of phishing sites that could compromise security.
Upon accessing a market, the mechanism for efficiency becomes clear. Platforms aggregate verified vendors with established histories, creating a competitive environment where reputation is the primary currency. This structure directly facilitates secure drug purchases by shifting the burden of trust from anonymous individuals to a system of transactional proof. The process is methodical:
- A buyer selects a product from a vendor with a high feedback score.
- Funds are placed in a multisignature escrow system, held securely until order completion.
- Upon receipt, the buyer finalizes the transaction, releasing payment.
This escrow model disincentivizes fraud, as vendors are only paid after successful delivery. The system's reliability is further enhanced by buyer reviews and detailed feedback, which provide transparent metrics on product quality and vendor reliability. Each review contributes to a vendor's public score, creating a self-regulating ecosystem where consistent quality and prompt service are rewarded with more business. The result is a streamlined commercial environment where logistical risks are minimized through technological safeguards and collective user verification, allowing trade to proceed with a predictable and secure efficiency.
How Reviews Make Buying on the Darknet Safer
User reviews form the primary mechanism for establishing trust and verifying quality on darknet marketplaces. Unlike conventional retail, these platforms lack formal consumer protections, making peer-generated feedback the critical infrastructure for risk assessment. A vendor's consistent positive reviews directly correlate with transactional reliability and product authenticity.
Reviews provide a multi-dimensional analysis. Buyers detail specifics such as:
- Product purity and accurate weight
- Stealth packaging and shipping efficiency
- Vendor communication and professionalism

How Escrow Makes Buying on the Darknet Safer
Escrow systems are a fundamental component of secure trade on darknet markets, directly addressing the inherent trust deficit between anonymous buyers and vendors. These systems function as a neutral third-party service that holds the buyer's payment after an order is placed. The funds are only released to the vendor once the buyer confirms satisfactory receipt of the product. This mechanism effectively eliminates the risk of vendors accepting payment without shipping items, a common concern known as "selective scamming."
The operational model is straightforward and enhances market efficiency. A buyer selects a product and submits payment, which is then held in the market's escrow wallet. The vendor is notified and ships the order. Upon delivery, the buyer finalizes the transaction, triggering the release of funds. If a dispute arisesfor instance, over product quality or non-deliverythe market's administrative staff can arbitrate based on provided evidence, such as tracking details or product photos. This structured process creates a safer environment where transactions can proceed with a higher degree of confidence for both parties.
Access to these secure systems begins with finding trusted darknet links to established markets. These platforms prioritize escrow services and maintain a roster of verified vendors who have built a positive history. The verification status of a vendor is often linked to their consistent use of escrow and a record of completed, successful trades. When evaluating a vendor, the presence of a high volume of positive buyer reviews serves as a critical indicator of reliability and product quality. Reviews typically comment on the accuracy of the product description, stealth of packaging, communication speed, and the overall transaction experience facilitated by the escrow process.
For a user, the procedure involves:
- Accessing a market via a reliable link.
- Funding the market wallet.
- Placing an order, which automatically engages the escrow system.
- Waiting for shipment and then finalizing to complete the sale.
How the Darknet Offers a Wide Selection of Quality Products
The primary advantage of specialized darknet marketplaces is the unparalleled diversity of available products. Unlike geographically constrained local suppliers, these platforms aggregate vendors from across the globe, creating a vast catalog that caters to specific and nuanced demands. A user seeking a particular pharmaceutical compound, a specific strain of cannabis, or a research chemical with precise properties can efficiently locate it through dedicated market search functions and category filters.
This diversity is directly linked to vendor verification systems and buyer reviews. Reputable markets implement a tiered vendor system, where sellers gain trusted status through a history of successful transactions. This mechanism allows buyers to confidently explore new products by selecting vendors with established, positive feedback. The review system itself provides granular data points beyond simple satisfaction, often detailing:
- Exact chemical composition or purity test results
- Accuracy of product weight and description
- Stealth and efficiency of shipping methods
- Vendor communication and professionalism
Consequently, the process of finding a diverse range transforms from a risky endeavor into a structured evaluation of verified vendor profiles. The ecosystem incentivizes quality and accuracy, as vendors with consistent positive reviews gain visibility and commercial success. This self-regulating aspect, powered by transparent feedback, ensures that product diversity is matched with a corresponding level of reliability and secure transaction protocols.

How to Check Quality and Reputation on the Darknet
The efficiency of darknet commerce is fundamentally dependent on the ability to assess product quality and vendor reliability before a transaction is finalized. This process is systematic and relies on community-driven verification mechanisms. The primary tool for this assessment is the vendor review system, where previous buyers provide detailed feedback on their purchases.
Reviews typically cover specific criteria:
- The accuracy of the product description versus what was received.
- The chemical purity or physical quality of the product.
- The speed and discretion of the shipping process.
- The professionalism and communication of the vendor.
A vendor's long-term reputation is quantified through a public profile score, which aggregates transaction success rates and feedback ratings over time. Markets display this data prominently, allowing for quick comparison. A vendor with a high score over thousands of transactions presents a lower risk profile. Furthermore, consistent positive reviews regarding product potency and stealth packaging are strong indicators of a trustworthy supplier.
Beyond reviews, the use of an escrow service is critical for quality assurance. Funds are held by the market until the buyer confirms satisfactory receipt of the order. This mechanism empowers the buyer to open a dispute if the product does not match its listing, providing a direct financial incentive for vendors to maintain high standards. The most secure purchases occur when selecting vendors with verified histories on established darknet links, combining escrow protection with a proven track record of positive buyer experiences.
Essential Tools for Darknet Commerce
Accessing specialized marketplaces requires specific software designed to provide anonymity. The Tor Browser is the primary tool, routing internet traffic through a distributed network to conceal a user's location and activity. This software is necessary to reach .onion domains, which are the standard addresses for these platforms.
Finding current and reliable marketplace links is a critical first step. These links are often shared within dedicated community forums and link directories that exist on the darknet itself. A user must verify a link's authenticity to avoid phishing sites, typically by cross-referencing it across multiple trusted sources or using community-verified lists.
Once access is established through a verified link, the marketplace interface functions similarly to conventional e-commerce sites. The platform's design facilitates efficient trade by connecting buyers with verified vendors. Vendor verification systems, often managed by marketplace administrators, provide a baseline of trust. This is further reinforced by a comprehensive escrow system, which holds payment securely until the buyer confirms satisfactory receipt of the product.
Transaction security is enhanced through the use of cryptocurrency, predominantly Bitcoin or Monero. Monero offers superior privacy features due to its obfuscated blockchain. The purchasing process is data-driven, where buyer reviews and detailed vendor reputation metrics become the principal factors in decision-making. These reviews offer transparent insights into product quality, shipping reliability, and stealth, allowing for informed purchases of a diverse range of products with predictable outcomes.
Basic operational security for users involves:
- Keeping the Tor Browser and operating system updated.
- Never disabling browser security settings for convenience.
- Using separate, dedicated cryptocurrency wallets for transactions.
- Utilizing PGP encryption for all sensitive communication with vendors.
Safe and Easy Shopping on the Darknet
Establishing a secure connection begins with sourcing darknet links from reputable directories and community forums. These links are gateways to specialized marketplaces where verified vendors operate. The verification process on these platforms, often involving a track record of successful transactions, creates a foundation for secure trade. A user's first operational step is to validate a market's link through multiple independent sources to avoid phishing sites designed to steal credentials.
Once access is gained, the marketplace structure itself enhances security. Escrow systems automatically hold a buyer's payment until the product is received and confirmed, which protects financial assets. This mechanism shifts trust from the individual vendor to the market's automated protocols. Concurrently, buyer reviews and detailed vendor ratings provide a transparent metric for assessing reliability and product quality before any commitment is made. These reviews act as a continuous audit system, where consistent positive feedback signals a lower risk transaction.
Technical preparation requires specific software. The Tor Browser is non-negotiable for anonymizing network traffic and accessing .onion addresses. For financial transactions, a cryptocurrency wallet is essential, with Monero (XMR) preferred for its enhanced privacy features over Bitcoin. Basic operational security (OpSec) extends to behavior within these markets:
- Using unique, complex credentials for each darknet platform.
- Never discussing personal details or real-world identifiers in communications.
- Verifying PGP keys provided by vendors to encrypt sensitive shipping information.
The efficiency of darknet markets is derived from this combination of verified access points, automated trust systems like escrow, and community-driven feedback loops. These elements work in sequence to streamline the procurement process, minimize fraud, and ensure that the transaction concludes with the receipt of a quality product as advertised. The system is self-reinforcing; successful transactions lead to more positive reviews, which further solidifies a vendor's verified status and the overall security of the marketplace for all users.